IT professionals can also take advantage of observing demonstrations of attacks to find out how facts behaves especially scenarios. Make time to look at demonstrations of the following attacks:
As a result, there is a compact opportunity for protection analysts to establish this traffic and take care of it to be a signature to disable a DDoS attack.
Shoppers who will’t use a corporation’s application or Web-site as common normally get angry and turn to the online world to trash the corporate.
A traditional DoS attack doesn’t use a number of, dispersed devices, nor will it center on products between the attacker and also the Corporation. These assaults also have a tendency not to employ several internet units.
Being aware of how you can determine these assaults aids you avoid them. Read more to familiarize by yourself with the categories of DDoS assaults you could possibly come upon from the cybersecurity discipline.
What's DDoS Attack: Attack Signs and symptoms And the way to Determine One among the biggest problems with pinpointing a DDoS assault is that the indicators are commonplace. A lot of the indications are similar to what technology customers come upon each day, like slow upload or obtain performance speeds, the website turning into unavailable to check out, a dropped Connection to the internet, unconventional media and information, or an excessive degree of spam.
Mitigating a DDoS attack is difficult simply because, as Beforehand noted, some attacks go ahead and take kind of web website traffic of the same kind that respectable people would produce. It would be simple to “stop” a DDoS assault on your internet site merely by blocking all HTTP requests, and indeed doing so could possibly be needed to keep the server from crashing.
DDoS attacks are malicious makes an attempt to overwhelm a target server or community with a large volume of website traffic, resulting in downtime, unavailability, or decreased performance.
Whatever the motivations that electrical power these assaults, hackers can certainly be hired to help launch a DDoS attack—offered only as guns for employ. People or complete professional groups can be found for employ about the darkish World wide web, usually under a provider design, comparable to that of infrastructure for a service (IaaS) or software program like a services (SaaS).
Do the job with ISPs, cloud suppliers as well as other services providers to determine the costs associated with the DDoS attack. Obtain a report from all suppliers. To move past the attack, you have to know just what exactly you happen to be managing and also have documentation As an instance it.
Inside a DDoS assault, cybercriminals benefit from usual behavior that occurs amongst network equipment and servers, generally focusing on the networking equipment that create a relationship to the net.
Create detailed protocols for backing up your information and utilizing it to mend your program when you’ve taken it offline. Establish communication protocols on your inside staff and also your buyers to reassure them about actions you’re getting to resolve the challenge.
Employers will need to know that you will be armed ddos web with the talents needed for combatting a DDoS attack. Adding these competencies in your toolset should help illustrate your ability to thwart assaults.
Though organizations in almost any industry are vulnerable, these sectors are matter to DDoS assaults most often:
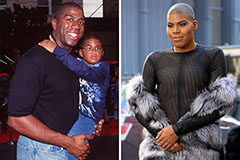 Earvin Johnson III Then & Now!
Earvin Johnson III Then & Now! Bernadette Peters Then & Now!
Bernadette Peters Then & Now! Erika Eleniak Then & Now!
Erika Eleniak Then & Now! Nadia Bjorlin Then & Now!
Nadia Bjorlin Then & Now! Ryan Phillippe Then & Now!
Ryan Phillippe Then & Now!